
- What is the dark web?
- How to get on the dark web
- The risks of accessing the dark web
-
How to stay safe on the dark web
- 1. Use a VPN to encrypt your internet traffic
- 2. Install antivirus software
- 3. Use safety and privacy-enhancing apps
- 4. Download Tor from its official website
- 5. Secure your computer before accessing the dark web
- 6. Change Tor’s security settings
- 7. Be wary of how you share your data on the dark web
- 8. Use cryptocurrency to pay for stuff
- 9. Close everything when you are done
- 10. (Optional) Use a mobile live OS
- 11. (Optional) Use a virtual machine
- Tor Over VPN vs. VPN Over Tor: What you need to know
- Dark web vs. deep web: Key differences
- History of the dark web: From birth to the present
- What can you expect on the dark web today?
- Is the dark web illegal?
- Conclusion: How to access the dark web safely
- FAQ
To access the dark web safely, you’ll need a specialized dark web browser called Tor, the specific Onion links you want to visit, and some safety tools. If it sounds complicated, we’ll guide you through it in a few simple steps:
- Subscribe to a VPN, which is vital when browsing the dark web as it encrypts your internet activity and protects you from malicious actors online.
- Download, install, and turn the VPN on. You might want to scroll down the list of servers and set up an “Onion over VPN” connection.
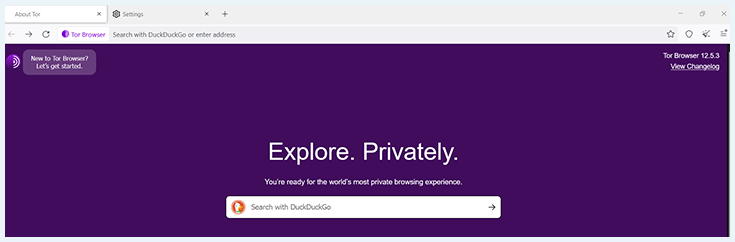
- Download and open the Tor browser. Getting on the dark web requires the use of this specialized browser.
- Change its security settings to “Safest.”
- Open the Hidden Wiki.
A good VPN is crucial when accessing the dark web. My top recommendation is NordVPN, which offers a number of dark web-specific features, such as Onion over VPN servers and robust AES 256-bit encryption.
Read this guide further to learn how to mitigate safety risks on the dark web.
What is the dark web?
The “dark web,” sometimes also called the “black web,” refers to all of the internet web pages that are not indexed by “normal” search engines and can generally not be accessed by a normal browser. These dark web links are also called “onion links” because they end in “.onion.”
So, how do you find the dark web if its pages are hidden? Well, you need a specialized browser to access dark web links: the Tor browser. Alternatively, you can also use Tor2web by using a normal browser and changing the ending of onion URLs slightly. However, we strongly recommend against this, as it doesn’t offer the same protection that the Tor dark web browser offers.
The dark web was originally created as an anonymity tool and is still used this way by many. It has proven useful to increase the safety of journalists and whistleblowers, for instance. It’s also a safe haven for free speech advocates and privacy-minded individuals.
Unfortunately, this part of the web is also home to many illegal activities. Dark web marketplaces sell all kinds of illegal items, ranging from firearms to narcotics and stolen credit card data.
The dark net has also been used for sharing illegal pornography and purchasing hacked accounts or software that can be used to break into someone’s bank account.
How to get on the dark web
Below, we’ll show you how to access the dark web. Make sure to follow all the steps outlined in this guide to ensure that you remain anonymous and safe.
- Download and install Tor from the Tor Project’s download page. The Tor browser is the safest way to access the dark web. It not only opens onion links but also protects you using strong encryption. If you’d like some help, check out our video below about installing Tor:
- Subscribe to a VPN, which hides your identity while browsing the dark web. We recommend NordVPN, as it uses industry-leading encryption to not only protect your data but also prevent government authorities and internet service providers from figuring out you’re accessing the dark web.
- Download and install NordVPN on the device you’re using to access the dark web.
- Connect to a VPN server. With NordVPN, you can choose its Onion over VPN servers, which automatically provide double protection when accessing the dark net.

- Launch Tor, the dark web browser.
- Adjust the browser’s security level to “Safest,” as shown below. We provide detailed instructions on changing Tor’s security settings later in the article.

- That’s it! You should be safe to access the dark web.
How to access dark websites
Knowing how to get on the dark web is one thing, but how do you search the dark web? Indeed, finding dark websites is another challenge altogether. Below, you can find our recommended dark web tools for exploring this part of the internet.
- The Hidden Wiki: This site is a dark web version of Wikipedia, linking to thousands of dark web pages. There are many copycat versions of the site, so make sure you only access it from this link: http://6nhmgdpnyoljh5uzr5kwlatx2u3diou4ldeommfxjz3wkhalzgjqxzqd.onion/
- Ahmia: Ahmia is a search engine specifically built for the dark web, so you can easily explore onion sites and search for content without having to know any specific onion links. You can visit the site here: http://msydqstlz2kzerdg.onion/
- Hidden Answers: Hidden Answers is a website that lets you ask any question without fear of censorship. Visit the site through this link:
- http://answerszuvs3gg2l64e6hmnryudl5zgrmwm3vh65hzszdghblddvfiqd.onion/
- DuckDuckGo: This is the best dark web search engine. However, some of its results may be dangerous, so be prudent when using this search engine. Here’s an “onion” link to the site: https://duckduckgogg42xjoc72x3sja7o78xcotqf6zif62g2otnrpgno7id.onion/
Note:
The dark websites above may link to webpages with illegal content, such as black market items, child pornography, or narcotics. The links above may also change without notice, as onion links get updated often.
Accessing the dark web requires prudence and care at every step. As such, it’s essential to know the risks of dark web access and how to protect yourself from them. We’ve visited and researched the dark web extensively, so below, we’ve outlined the risks we think you should be aware of.
The risks of accessing the dark web
Now that you know how to access the dark web, you should also consider the risks you may encounter once you’re there. We understand you’re excited to access the dark web now that you’ve found out how to enter the dark web. However, we urge you to study the infographic on dark web risks below.

The dark web is a complex place where a lot can go wrong when you don’t do proper research on how to access the dark web safely. It is full of scammers, malware, and phishing websites — and these are just a few of the dangers. The main risks of visiting the dark web can be found in the table below.
| Dark web risk | Explanation |
|---|---|
| Scams and phishing attempts | Dark web criminals can manipulate you into handing over your sensitive data, spending money on a fake product, or downloading malware on your device through malicious pages, links, and attachments. |
| Botnets | Some malware that’s spread on the dark web can take over large numbers of devices and use them for mass attacks. If your device is used this way, its performance will decrease, and you might get unwillingly involved in illegal activities. |
| Copyright-infringing and disturbing content | Some dark web pages contain illegal and disturbing content, such as extreme pornography or adult content showing minors, violent and explicit videos depicting executions or torture, and copyrighted movies and shows. This content can wear on your mental state and get you into legal trouble. |
| Illegal activity | The dark web is home to various illegal marketplaces. These platforms might be used to sell drugs, arms, or any other illegal goods. Don’t get mixed up with these platforms and the people on them to avoid legal issues. |
| Webcam hacking | Webcam hacking, or camfecting, involves cybercriminals taking over your device’s camera or cameras through malware. Since the dark web is much more unregulated than the surface web, you might be more likely to come into contact with camfecting malware on the dark web. |
| Suspicious links | Over 70% of online attacks are due to human error, and one of the most common human errors is clicking on the wrong link. With so many phishers on the dark web, you have to be extra careful to avoid suspicious links. |
Now that we’ve looked at how to enter the dark web and have gone over some of the gravest risks of doing so, we’ll give you some tips on how to access the dark web safely.
How to stay safe on the dark web

1. Use a VPN to encrypt your internet traffic
If you’re wondering how to get on the dark web as safely as possible, we recommend getting a VPN to use alongside Tor. VPNs encrypt your web traffic and hide your IP address, adding an extra layer of protection.
Moreover, a VPN will help to protect your traffic before it reaches the first server within the Tor network, protecting you from any malicious Tor server owners.
Unfortunately, not every VPN provider is reliable. This is especially true for free VPNs. To stay safe on the dark web, we prefer using a premium VPN service like NordVPN. The latter offers military-grade encryption and great anonymity. The VPN is currently offering a great discount.
To access the dark web from a country where the Tor Network is banned or restricted, we suggest using obfuscated servers. These servers combat deep packet inspection, a surveillance method ISPs and the government use to determine if a VPN is being used.
NordVPN offers obfuscated servers in several countries, including Germany, Spain, Hong Kong, and the United States.
2. Install antivirus software
A VPN protects your internet activity from prying eyes. However, you also need to protect your system against malware you might encounter on the dark web. An antivirus is crucial for this. It will scan the pages you visit and all the files you download for threats.
Norton 360, our leading antivirus, prevents malicious files from being downloaded on your devices via its firewall. It also offers a dedicated dark web monitor that alerts you if your stolen data is found in a dark web data leak.
3. Use safety and privacy-enhancing apps
The combination of a VPN and antivirus scanner will prevent most threats when you access the dark web. However, if you plan on spending extended time exploring the dark net, we advise you to equip yourself with a robust suite of additional safety and privacy-enhancing apps, including:
- A private, good dark web search engine like DuckDuckGo: DuckDuckGo is one of the best dark web search engines out there. Unlike most other search engines, DuckDuckGo also indexes the onion links that the dark web consists of. The onion address for DuckDuckGo is https://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion/.
- A password manager: A good password manager is needed to secure all of your passwords, on and off the dark web. We recommend our number one password manager: NordPass.
- Anonymous file-sharing apps: These types of apps allow you to share files securely and have private conversations with friends on Tor. A commonly used app is OnionShare.
- A secure messaging app: If you want to send messages that are encrypted, safe apps like Signal can help you do that.
- An anonymous email address: If you want to send emails that cannot be traced in any way, then opt for an anonymous email provider like ProtonMail.
4. Download Tor from its official website
People looking to access the dark web should be careful when downloading the Tor browser because it’s a prime target for hackers. Fake versions of Tor breach users’ security before they even access the dark web, or monitor the behavior of a user while on the dark web.
Always download the Tor browser from its official website: https://www.torproject.org/. Make sure you download the latest version, and always keep it up-to-date.
5. Secure your computer before accessing the dark web
Before you open the Tor dark web browser and go to the dark web, you should:
- Close all non-essential apps on your device, like Netflix and Spotify.
- Cover your webcam with a piece of paper to protect your privacy in case your webcam gets hacked.
- Turn off your location on your device.
- For Windows 10 and 11: Settings > Privacy > Location > Turn off location + Erase location history
- For macOS: System Preferences > Security & Privacy panel > Privacy > Uncheck “Enable Location Services”
6. Change Tor’s security settings
You can change Tor’s level of security to “Safer” or “Safest.” Naturally, the highest setting is the safest. However, this setting significantly slows down your internet connection and causes some pages and dark web websites to load incorrectly.
The highest security setting will disable most video and audio formats, some fonts, and even icons. JavaScript is also disabled, and images may not display correctly. If you’re willing to sacrifice that for your safety, here’s what you need to do:
- Open the Tor browser.
- Click on the hamburger menu in the top-right corner and select “Settings.”
- Click on “Privacy and Security.”
- Scroll down to the “Security” heading.

- Select “Safer” or “Safest.”
The “Safer” option only disables JavaScript on websites that aren’t HTTPS protected. “Safest” disables JavaScript on all websites.
Manually turn off scripts in Tor
You can also manually turn off scripts in Tor without changing Tor’s general security level. Here’s how it works:
- Enter this address into the Tor browser: “about:config”.
- You’ll be notified that changing advanced settings can impact Tor’s performance and security. Click “Accept the Risk and Continue.”

- Now type the following into the search bar: “xpinstall.signatures.required.”
- Click on the little gray icon at the far right of your screen to change the value of the configuration.
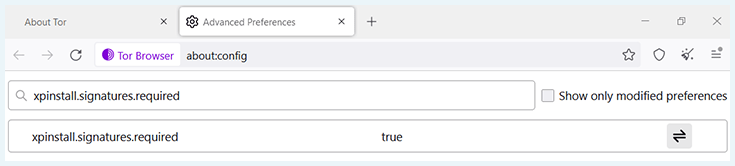
- Check whether the value now reads “falls.” If so, you have successfully disabled JavaScript.
It is important to change these settings because websites often run scripts without notifying you. Note that you won’t need to do this if you have already enabled the safety settings on Tor, as the scripts are already turned off.
Change other security settings
Tor also has other security settings that you might want to consider, like:
- The option to clear all of your cookies
- The option to clear your browsing history
- A setting that warns you about potentially deceptive content

If you visit the dark web, we highly recommend that you enable this setting and clear your cookies and history regularly.
You’ll find all of these security settings under Settings > Privacy & Security.
7. Be wary of how you share your data on the dark web
Revealing personal information about yourself on the dark web can have serious ramifications, as it allows hackers to identify and target you. It’s prudent to limit your information sharing on the dark web.
Here are a few tips on how you can do the above:
- Don’t share your credentials with anyone, no matter what they say.
- Don’t click on dark web links unless you know exactly where they’ll take you.
- Only access sites from trustworthy indexes, like The Hidden Wiki.
- Don’t change Tor’s screen size because if you do, there’s a chance you’ll have a unique viewport size, making you easy to identify.
- Don’t type straight into the Tor browser, as typing patterns can be used to identify you. So write your queries out in a Notes app, then copy and paste them into Tor.
- Analyze your browser’s identity with Cover Your Tracks.
8. Use cryptocurrency to pay for stuff
There are tons of dark web commerce sites where you can buy legal or illegal goods. The most infamous example was “The Silk Road,” which has long been shut down. However, new markets pop up all the time.
We advise you not to purchase anything illegal. If you want to buy legal items, only pay with cryptocurrency when visiting dark websites. It’s the only way to stay anonymous and protect your funds.
Bitcoin is the most well-known cryptocurrency. However, Bitcoin has a number of privacy issues, such as address reuse, connected nodes, tracking cookies, and blockchain analytics, that allow Bitcoin users’ identities to be revealed. Instead, you should use a privacy-focused crypto like Monero.
9. Close everything when you are done
When you’re done accessing the dark web, make sure you close the following:
- All of your Tor browser windows
- The Tor dark web browser
- Tails or any other operating system used to access the dark web
If you want to be completely safe, you should also clear browsing cookies and history. Check out “Change other security settings” above to learn how to do so.
Now, do a complete reboot of your system. This ensures you won’t be tracked by any scripts or cookies you might’ve enabled in your browsing. It may take a while, but it’s an important step.
10. (Optional) Use a mobile live OS
If you’re wondering how to get on the dark web safely, you should know that the more anonymous you are, the better. That’s why you might want to use a portable operating system when accessing Tor. Operating systems like Windows 10 or 11 are not very well-suited for privacy because:
- Your data is continually synced, meaning your browser history, open websites, app settings, and Wi-Fi hotspots are all tracked.
- Your device is automatically linked to a unique advertising ID for third parties.
- Cortana collects data, such as your keystrokes, search results, microphone audio messages, calendar information, music playlists, and even your online purchases.
- Microsoft can collect all sorts of personal data, like your identity, your passwords, habits and interests, user data, contacts, and locations.
If a hacker manages to get into your system via the dark web, all of this information is in danger. Comparatively, portable operating systems like Tails, Whonix, ZeusGuard, and Qubes OS prevent unwarranted data collection and surveillance, limiting the data at risk in case of a breach.
Note, however, that these are difficult to install. So we do not recommend you do this if you just want to visit the dark web once or twice.
11. (Optional) Use a virtual machine
If you want to be 100% sure you won’t install any malware on your PC while on the dark web, you can use a virtual machine (VM). In short, a virtual machine is an emulation of an actual PC using your existing computer or the cloud.
Virtualization apps will dedicate a portion of a computer’s resources to simulating a separate device. The word “separate” is key here, as this isolation from your “real device” will protect the latter in case anything goes wrong. If you click on the wrong link, install something suspicious, or encounter any other danger, you can just close the virtual machine, and you’re done.
VMs can be complicated to set up. But there are a lot of apps, like Azure Virtual Machine, that simplify the process a lot.
Keep in mind:
Depending on the VM solution you use, you can still harm your network, which can pose risks to your other devices as well.
Tor Over VPN vs. VPN Over Tor: What you need to know
The specialized browser people use to access the dark web is the Tor browser. It encrypts and decrypts traffic to access dark web websites. However, it’s not the same as using a virtual private network (VPN) — the two have different security protocols and encryption methods.

There are two ways to use a VPN and Tor together:
- Tor over VPN: When you first connect to a VPN and then open the Tor network
- VPN over Tor: When you open Tor and then connect to a VPN
Which of the methods above is the safest way to access the dark web? If you want to get on the dark web, you should use Tor over VPN. If you want to use Tor with websites that normally block its network, you need to use VPN over Tor. In 9 out of 10 cases, Tor over VPN is the right choice.
If you get NordVPN, you can also use the Tor network whenever you want with its Onion over VPN servers. These are special servers from NordVPN that first hide your IP address and then route your traffic through the Tor network.

From our experience, these servers aren’t as fast as regular VPN servers or double VPN servers. However, they’re perfect for complete anonymity. If you want to stay safe online, get NordVPN now at a 76% discount.
Dark web vs. deep web: Key differences
The deep web refers to all the web content not indexed by search engines. Note that, unlike dark web pages, this web content can’t be accessed through any web browser, not even the Tor browser.
Most of the content on the internet is part of the deep web. It includes your email inbox, company databases, member-only areas, and anything you won’t find through Google.
To access deep web pages, you need the specific link to the page you want to access. Often, you also need to provide some kind of authentication, such as a password.
The dark web is a very small part of the deep web. Unlike the deep web, you typically don’t need any kind of authentication to access the dark web. However, you need the specific onion links for the dark web sites you want to visit.
Here’s an infographic to make the “webs” easier to visualize:

History of the dark web: From birth to the present
Below, we’ll provide a nice infographic outlining the developments that led to the creation of the dark web as we know it today. We’ll also provide a brief written overview of key events.
- In 1969, the ARPANET was created to help the US military securely exchange sensitive information. The ARPANET was the precursor to the modern internet.
- In 1993, ten years after its birth, the modern internet became available in many countries around the world.
- In 2002, the US government-backed Tor browser was officially launched to provide a more secure way to communicate online. However, over the years that followed, more and more criminals started abusing its privacy features for illicit activities.
- Bitcoin’s creation in 2008 finally provided users with a way to transact anonymously on the dark web. Unfortunately, this also resulted in the emergence of many illegal dark web markets.
- In the second decade of this century, governments around the world started combating illegal dark web markets, closing down key players like Silk Road, Silk Road 2.0, Alphabay, and Hansa. Illegal activity persists on the dark web, but perpetrators no longer have free reign.
Of course, the above is only a very brief overview of the history of the dark web. For more information, you can check out our comprehensive guide to the dark web.
What can you expect on the dark web today?
Like the regular internet, the dark web is home to all types of sites.
If you don’t venture far, you’ll find everyday sites like forums, chat rooms, or dark web torrent websites. To many people, the dark web is just like the surface web — a place where they watch funny videos, chat with like-minded people, and read the news.
However, thanks to its potential for anonymity, the dark web also features a lot of sites you won’t find on the surface web. For instance, the dark web is where a lot of journalists exchange information anonymously. Sites like ProPublica and Secure Drop are fundamental to investigative journalism.
Unfortunately, the dark web’s criminal underbelly is very real. You can find black markets where people advertise drugs, guns, stolen IDs, and more. There is also an abundance of disturbing content, like explicitly violent videos or illegal pornography.
Some of the illicit things you can find on the dark web include:
- HIPAA-sensitive information, such as medical records
- Stolen credit card numbers
- Stolen financial account details
- Sensitive legal documentation
- Malware, botnets, Trojans, keyloggers, and other harmful exploits
- Services like corporate espionage or DDoS targeting
- Child pornography
- Videos of homicides or other violent events
Is the dark web illegal?
Having read the previous section, you may wonder if accessing the dark web is illegal. Connecting to the dark web is generally not illegal in itself. Using the Tor browser for dark web access is legal in most countries.
There are exceptions, however. Countries like Russia, China, and Turkmenistan have blocked the Tor network. These countries also tend to have more far-reaching internet restrictions. Please note that going on the dark web or using the Tor network in these countries could land you in trouble.
Please note:
If you do anything illegal on the dark web, you can still be prosecuted.
Conclusion: How to access the dark web safely
Because the risk of encountering malware is significantly higher on the dark web, to stay protected when accessing it, always pair a reliable VPN with a high-quality antivirus. The VPN will hide your IP address and traffic, while the antivirus will protect your device against infected downloads.
We recommend using NordVPN and Norton 360, as they ensure that malicious threats on the dark web can’t harm you. You can try NordVPN risk-free now by taking advantage of its 30-day money-back guarantee.
For more guides and tips about the dark web, read our other pieces as well:
- Dark Web Facts vs. Myths: What You Need to Know
- The Best Dark Web Documentaries
- How to Stay Safe on Dark Web Marketplaces
FAQ
Do you want to know how to get on the dark web? Here are some frequently asked questions and answers about the dark web and how to access it.
Accessing the dark web requires a specialized browser called Tor, which enables access to sites. However, if you want to stay safe on the dark web, you also need a VPN that provides an additional layer of security.
Most people use the Tor browser to visit dark web sites. The Tor browser is free and legal to use in most parts of the world. However, some countries like China, Russia, and Belarus have banned it.
A dark web site is a website that has a .onion extension in its URL. These are only accessible through the Tor browser, and they offer enhanced anonymity to their users. But that’s all they have in common. You can find almost anything on the dark web.
To access a dark web website, you’ll need the Tor browser, as .onion sites are not accessible with a regular browser. After you get the Tor browser, make sure you only access sites from trustworthy sources, like the Hidden Wiki.
The Hidden Wiki is a page on the dark web that looks like a Wikipedia page. It’s the best index of popular sites on the dark web, and you can access it with this link: http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion/wiki/
DuckDuckGo is a search engine just like Google and Bing. However, DuckDuckGo doesn’t keep track of your usage and also shows .onion websites in its results.





Thanks for the information. I'm not going to access but really enjoyed understanding what it is all about.
Thank you, Tanya! We're glad we could help satisfy your curiosity :)
How do I get URL to websites in dark web
A good source to start is the Hidden Wiki. We have an article with some Dark Web URLs and a link to the Hidden Wiki here: sites to visit on the Dark Web.
Great info here. I have always wanted to visit TDW, just out of curiosity mostly. However, I am never able to fully commit because as you said, you can never be guaranteed 100% anonymity or safety. I'm not worried about being anonymous so much as I do not plan to visit any sites that promote illegal activity, but I understand it is imperative to remain anonymous anyway to avoid identity theft and scammers/hackers. Overall this info is the best I've see on the subject!
Can i know the reason why 'it is advisable not to dive deeply in some parts of the dark web'?
Because some sites deal with topics that are illegal and could get you into legal trouble (drug marketplaces, gun marketplaces etc.)
Is there anyone who tutors people locally for a fee in regards to this? If so, how would one find these people? Any ideas, any references?
We wouldn't know about any local tutors, since we don't (have to) know where you currently are. There are probably some online courses to be found, although when it comes to the dark web, it's especially important to always make sure you're getting the right, reliable information. We'd advise you to read guides like the one in this article and go from there. If you want to make sure of the quality, cross-referencing different articles is always helpful. Besides that, we'd also advise you not to dive too deeply in some (especially dark) parts of the dark web. Using the BBC Mirror or other informative or otherwise interesting pages is fine, of course.